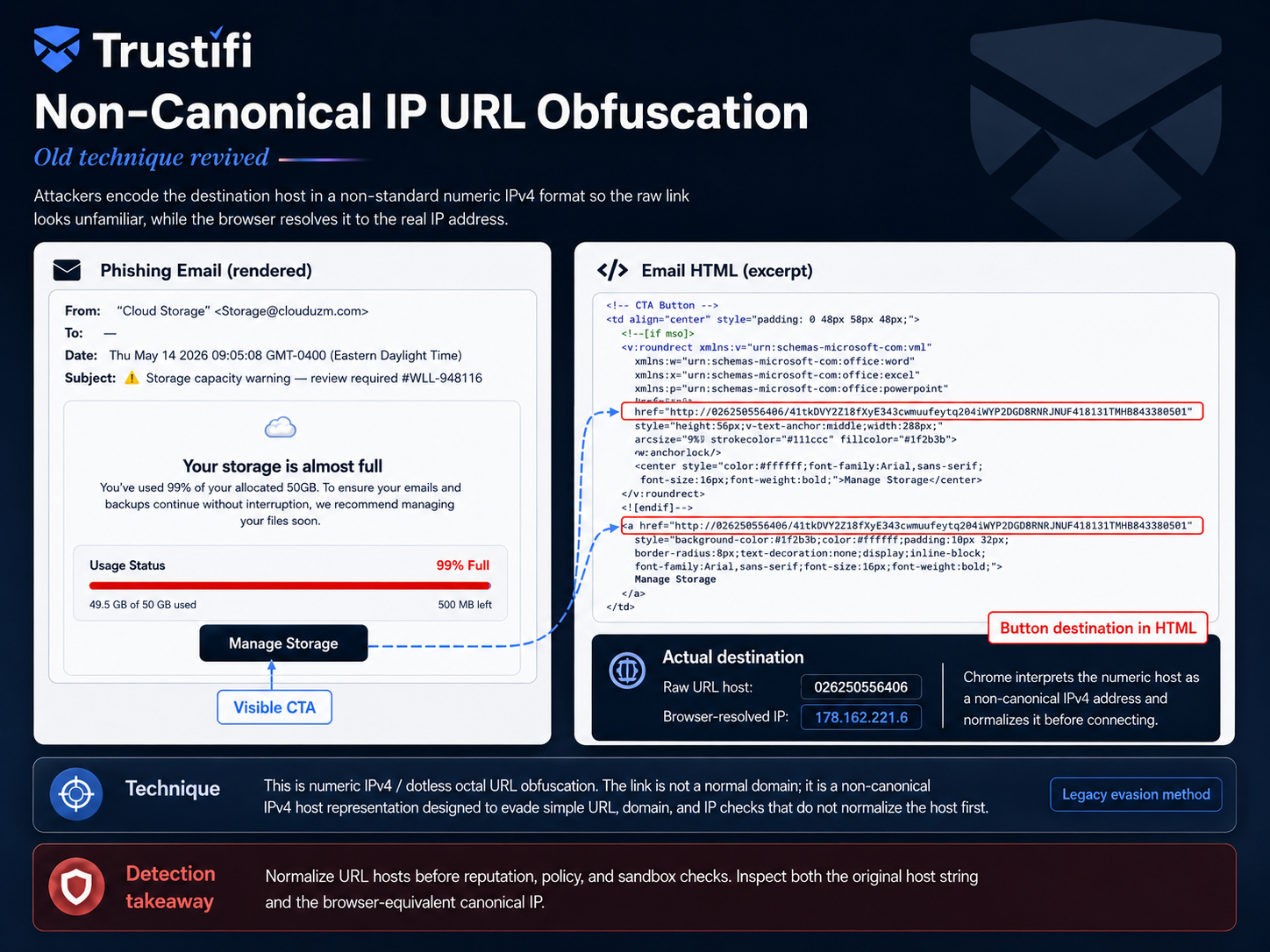
HostMimic: Old Technique Revived – Non-Canonical IP URL Obfuscation
HostMimic: Old Technique Revived – Non-Canonical IP URL Obfuscation Trustifi observed multiple quarantined phishing emails using a very old but still effective URL evasion technique: Non-Canonical IPv4 URL Obfuscation. We’re calling this observed phishing pattern HostMimic. The emails looked like...








