Who Is the Target of Phishing Scams?
Phishers target everyone, not just tech companies. They’re attacking people from every walk of life. People who contact you have many years of claiming to be old-school pals; chances are you never went to the same school. Phishers trove through...
Stopping Zero-Click Email Attacks
Zero-day attacks remain a global security challenge, even with continued patching and software updates for endpoints, mobile devices, and systems. The hackers develop an exploit against exposed attack surfaces with a known vulnerability while catching clients between patch cycles. Email...
How to Recover from an Email Phishing Attack
Recovering from any attack, cyber or otherwise, is a journey, always challenging to accomplish in a few steps. Organizations affected by email phishing attacks become concerned in several areas within their enterprise, including Data Exfiltration Identity Theft Disruption of Business...
What is the CPRA
The California Privacy Rights Act (CPRA) amends the California Consumer Privacy Act (CCPA) by strengthening Consumer Privacy Rights and tightening business regulations for personal information use. This article will discuss the details of CPRA and the changes compared to the...
What is Fileless Malware, and How Can It be Stopped?
Fileless malware attacks computers with legitimate programs that use standard software. This challenging malware lives in Random Access Memory space, making it harder to detect. Users clicking on malicious files or downloading suspicious attachments in an email will lead to...
What is Malware? – Where, How, and Why?
Hacks and malware are related and often involve malicious software delivered by email phishing attacks and message attachments. Even novice cyber-crooks can easily access malicious source codes to launch ransomware infection attacks. Using malware programs helps hackers better avoid the...
ChatGPT-3 AI Perfection is Imperfection in Disguise
We often criticize chatbots as being unreliable and can give inaccurate answers in some ways. Since the ChatGPT training process uses a trial-and-error system, its accuracy only depends on data and algorithms. Organizations considering leveraging Artificial intelligence(AI) tools like ChatGPT...
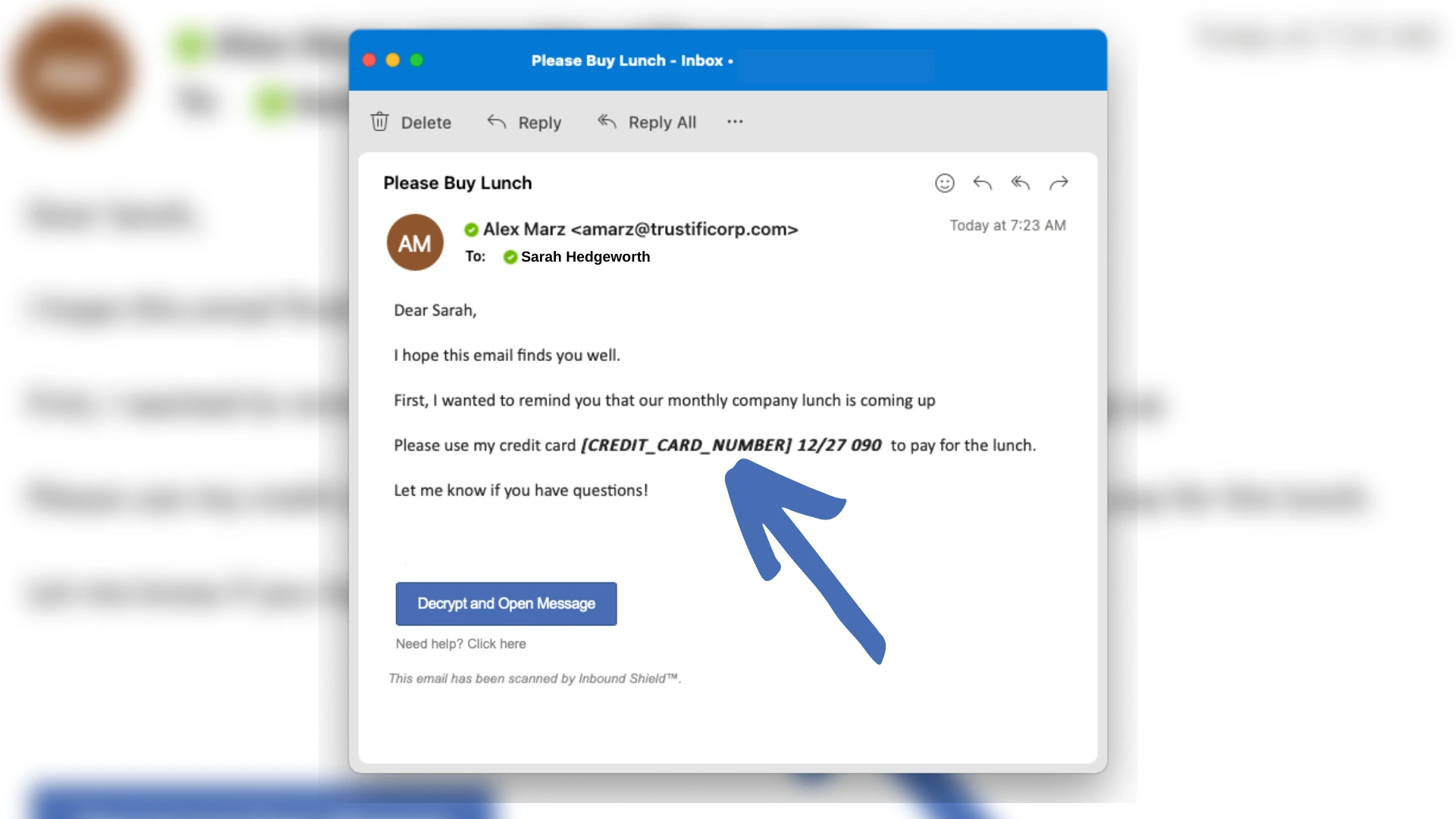
How Does Tokenization Improve Email Productivity?
Data Tokenization has become increasingly critical for organizations needing to meet compliance obligations while preventing unauthorized access to corporate data without always encrypting every email. Meet Trustifi’s Tokenization. Trustifi is the only company to offer data tokenization for the email...
What is Pharming?
If you think you have found some pharming websites, you can contact your internet service provider (ISP). Ultimately, it is their job to detect and take down these malicious websites. However, with the ever-growing number of cybercriminals, there are bound...