What is the Best Phishing Software for Your Business in 2024?
To safeguard your business from malicious emails and a phishing frenzy, it is crucial to identify vulnerabilities, assess potential risks, and choose suitable protective measures that align with your business requirements. Trustifi, a global leader in email security, understands the...
What is an Email Phishing Attack? How to Prevent New Ones?
Once hackers realize how lucrative email phishing has become, they focus on attack vectors, including financial fraud, business email compromise, and romance scams. Trustifi, a global leader in email security powered by artificial intelligence(AI), continues to lead the market with...
What is the Risk of Quishing QR Code Attacks Within Emails?
The FBI reported in September 2023 that threat actors continue to plant (QR) in several public areas, encouraging users to scan for phishing link exploits. Trustifi, a leader in advanced AI-email security’s security operation (SecOps) teams, monitors all attacks against...
Financial Losses Due to Email Phishing Attacks
The rise in phishing attacks costs organizations millions of dollars each year because of fines, the cost of remediation, and the long-term impact on their brand. Trustifi, a leader in email security powered by AI, understands the continuous challenge of...
Trustifi’s Anti-Bot Detection Stops Targeted Attacks Shrouded Inside of Known Global Sites
Over the past several weeks, Trustifi has identified an increase of 250%-300% in email attacks from hackers that impersonate the targeted campaign while they shrouded themselves inside known global sites (AWS/YouTube/Google Translate) to host their malicious links. This combination is...
Spoof! You’ve Been Hacked!
How did the hackers steal my email account? Panic is often a normal part of the reaction when people discover their email accounts have been used to send fake emails, online scams, or spoof emails. Calm is best, though; in...
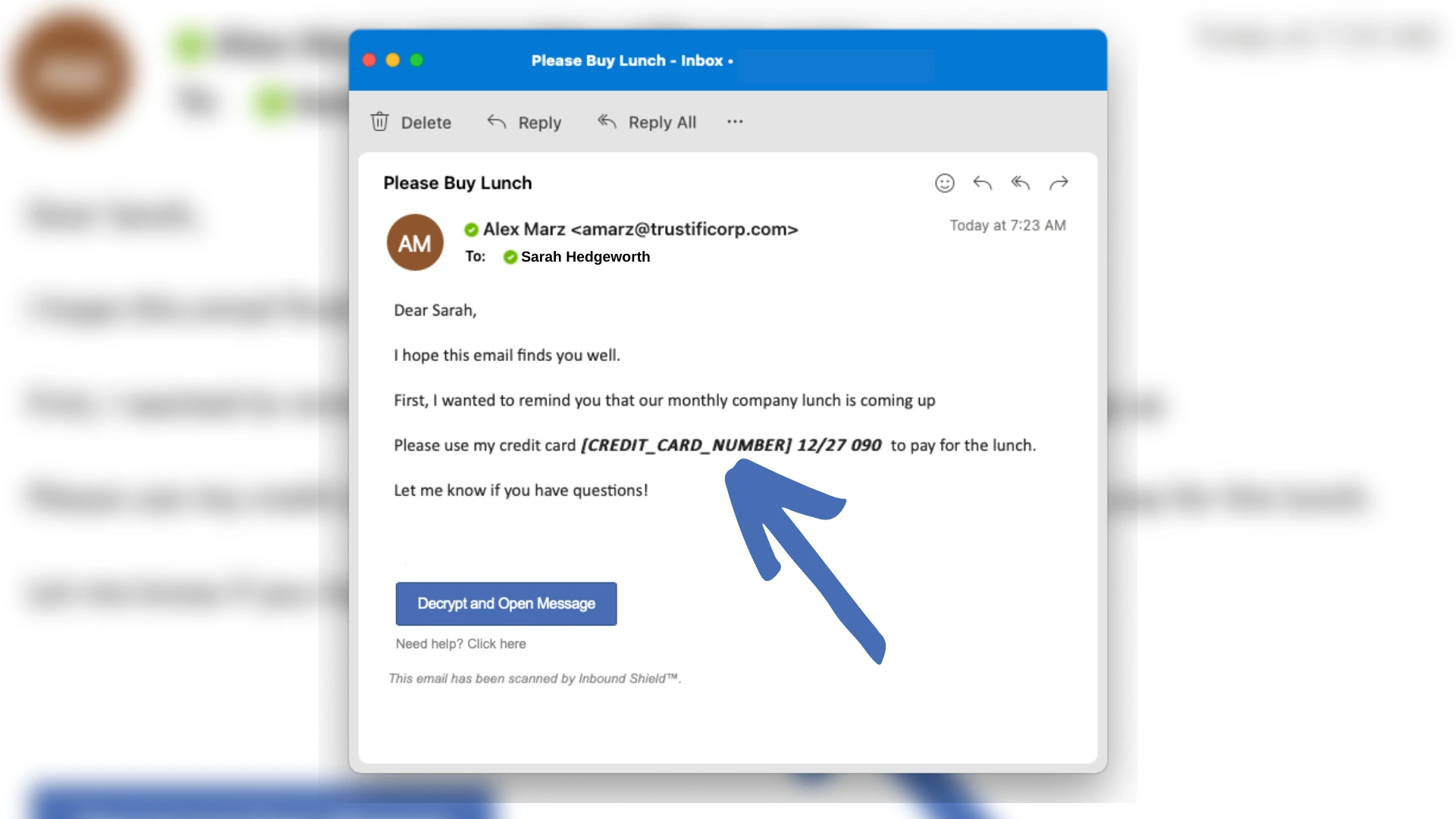
How Does Tokenization Improve Email Productivity?
Data Tokenization has become increasingly critical for organizations needing to meet compliance obligations while preventing unauthorized access to corporate data without always encrypting every email. Meet Trustifi’s Tokenization. Trustifi is the only company to offer data tokenization for the email...
How to Send a Secure Email Attachment
Most organizations at one time have lost critical data through the email channel. The data sets include intellectual property, confidential spreadsheets with financial information, and accidental sharing of employee information. Malicious insider threats from disgruntled employees were attempting to copy...
Crypto Malware vs Ransomware: What Are the Main Differences?
Mining cryptocurrencies require extensive computational power and time. When the complexity of the mining becomes more intense, more energy is needed.